Overview
What Is Robotic Perimeter Security?
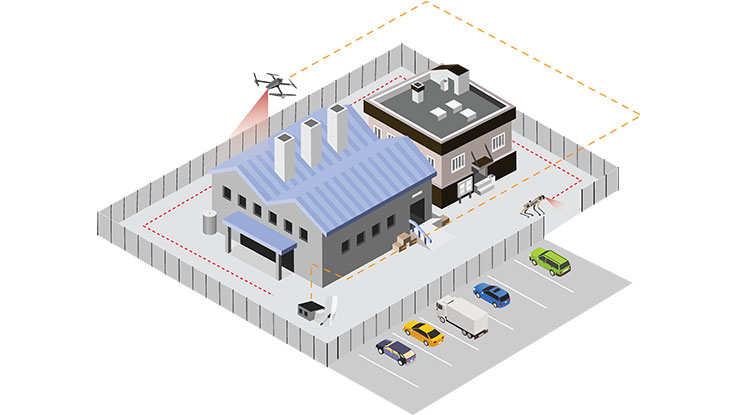
The leveraging of aerial and/or ground robotics as part of formal perimeter security operations. Robotic perimeter security includes a central command station and involves security robots for automated response protocols, pre-programmed patrol missions, and/or manual mission setting
- Deploy Ground And Aerial Drone Assets
- Easily Program Patrol And Response Mission Sets
- Remotely Monitor, Respond, And Report
Automated aerial and ground robotic security guard posts. We build the best and partner with the best to provide superior technology, capability, and service.
Automated Security Robots
Modernize Your Security Operations
A Closer Look
Aerial Robotics
- Rapid First Response
In an emergency situation, immediately launch a drone to act as an aerial first responder and provide high-quality intelligence to inform a response. - Safe And Compliant
Our in-house experts ensure your automated drone program is safe and compliant. Our technology is built around the stringent requirements of the aerospace industry. - Data Security
Our drones are designed, engineered, and manufactured by us in Philadelphia, PA. We offer 256-bit AES data encryption to all of our customers. - Battery Swap Automation
Our drones take off from and land on our custom-built base station, DroneHome, for autonomous battery swapping to maximize response capabilities.
Ground Robotics
- All-Terrain
The DroneDog can easily navigate stairs, grass, gravel, rocky, hilly, and icy terrain - High Endurance
Automate entire perimeter sweeps with a 90 minute average battery life - Data-Driven
Unlock artificial intelligence and immediate software upgrades with advanced, platform-based security solutions - Scalable
Easily integrate multiple units for advanced perimeter security applications
Details
Outperform 24/7 guard posts
Access advanced data analytics
Receive continuous software upgrades
Patrol with thermal and electro-optical camera systems
Operate remotely, anywhere in the world
Inform a response with high-quality data
Use historical data to build a security model around AI/ML
Automate the dull, dirty, and dangerous jobs
Images
Videos

Sorry, you must be logged in to view the rest of this page
Please log in or create an account to view more details.
Log in or Sign UpCustomers and Partners
Documents

Sorry, you must be logged in to view the rest of this page
Please log in or create an account to view more details.
Log in or Sign UpExpert Analysis

Sorry, you must be logged in to view the rest of this page
Please log in or create an account to view more details.
Log in or Sign Up